AI autonomy is probabilistic
Enterprise operations need explicit routing, ownership, and review before high-impact actions run.
Governance infrastructure for autonomous AI operations
AI teams execute work, but every mission stays reviewable, governed, and accountable.
Built for CTOs, security leaders, risk teams, and platform engineers running regulated AI operations.
Every governed mission leaves a reusable decision record linked to evidence, policy, and outcome.
Models generate probabilities. Enterprise operations require explicit routing, accountable ownership, and evidence that survives review.
Enterprise operations need explicit routing, ownership, and review before high-impact actions run.
Leaders need decisions that survive internal review, external audit, and operational escalation.
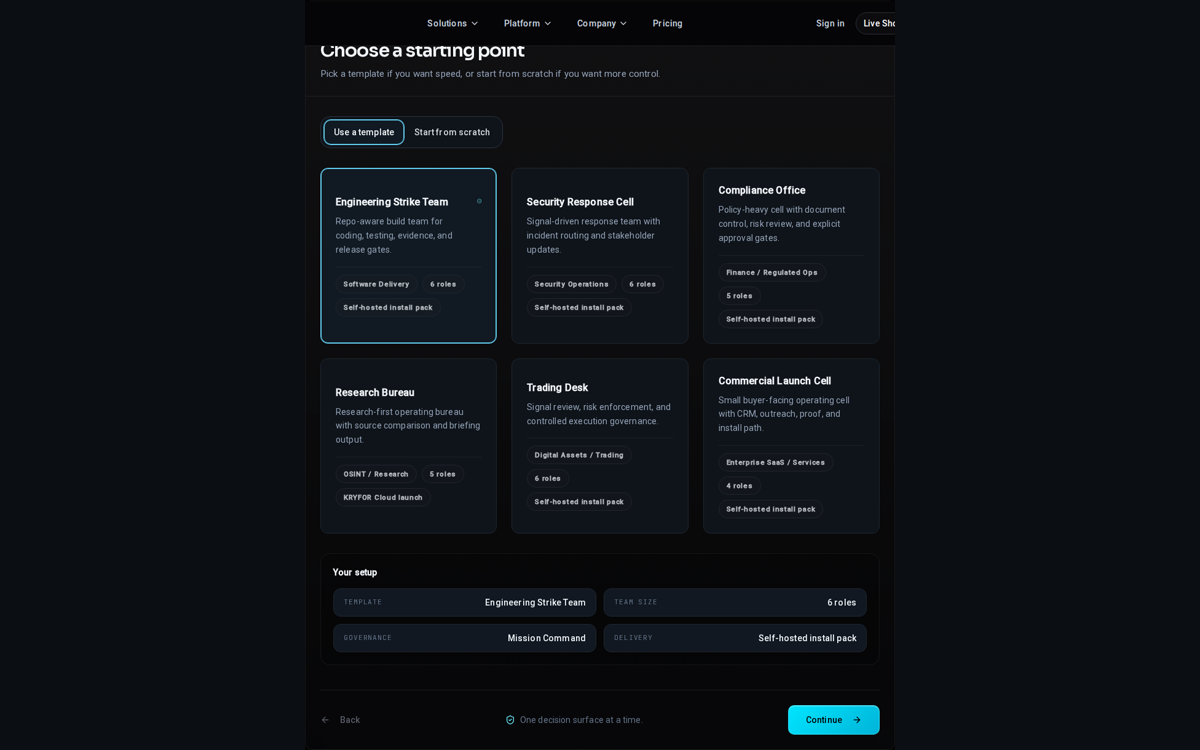
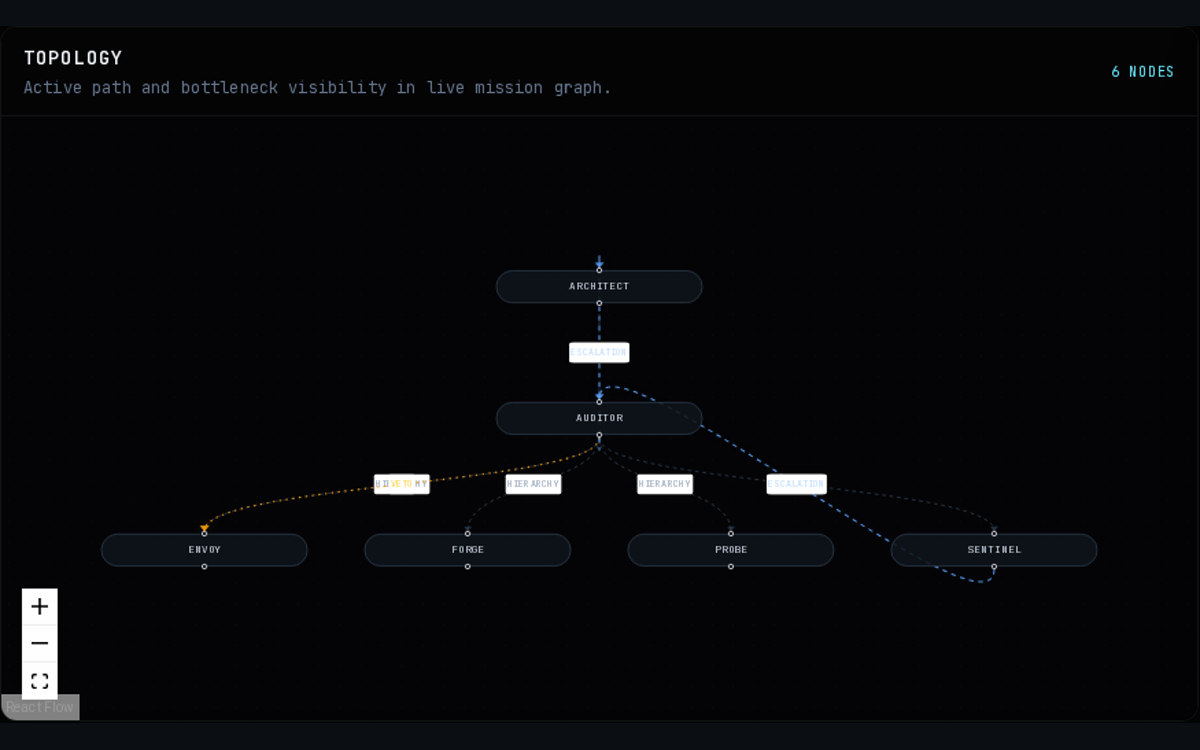
Mission graphs, policy gates, and evidence logs turn autonomous runs into controlled operating systems.
KRYFOR sits between autonomous execution and enterprise operations, turning agent activity into reviewable operating systems.
Layer 1
Agents
Layer 2
Mission graph
Layer 3
Governance layer
Layer 4
Policy gates
Layer 5
Execution systems
Layer 6
Evidence log
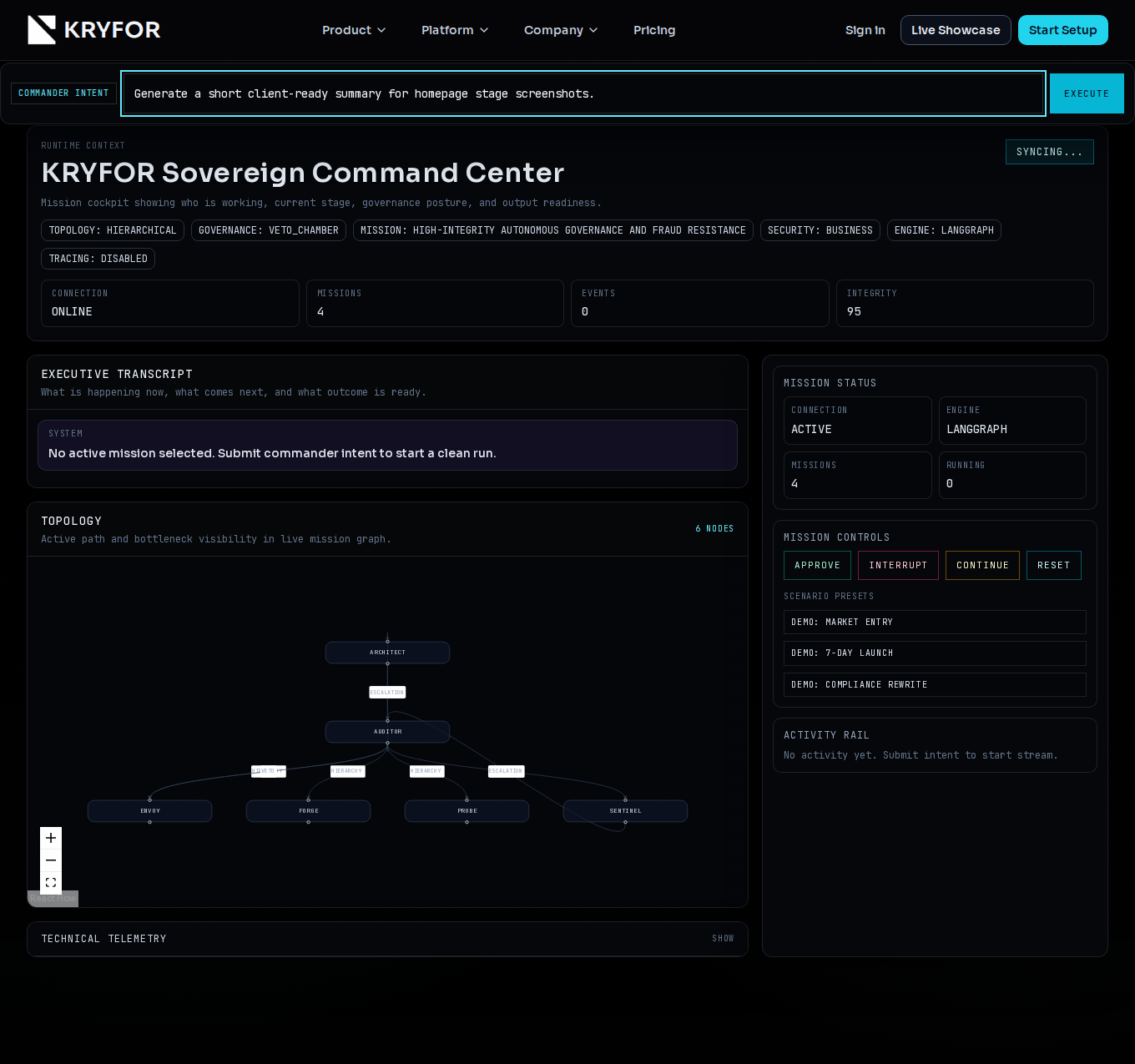
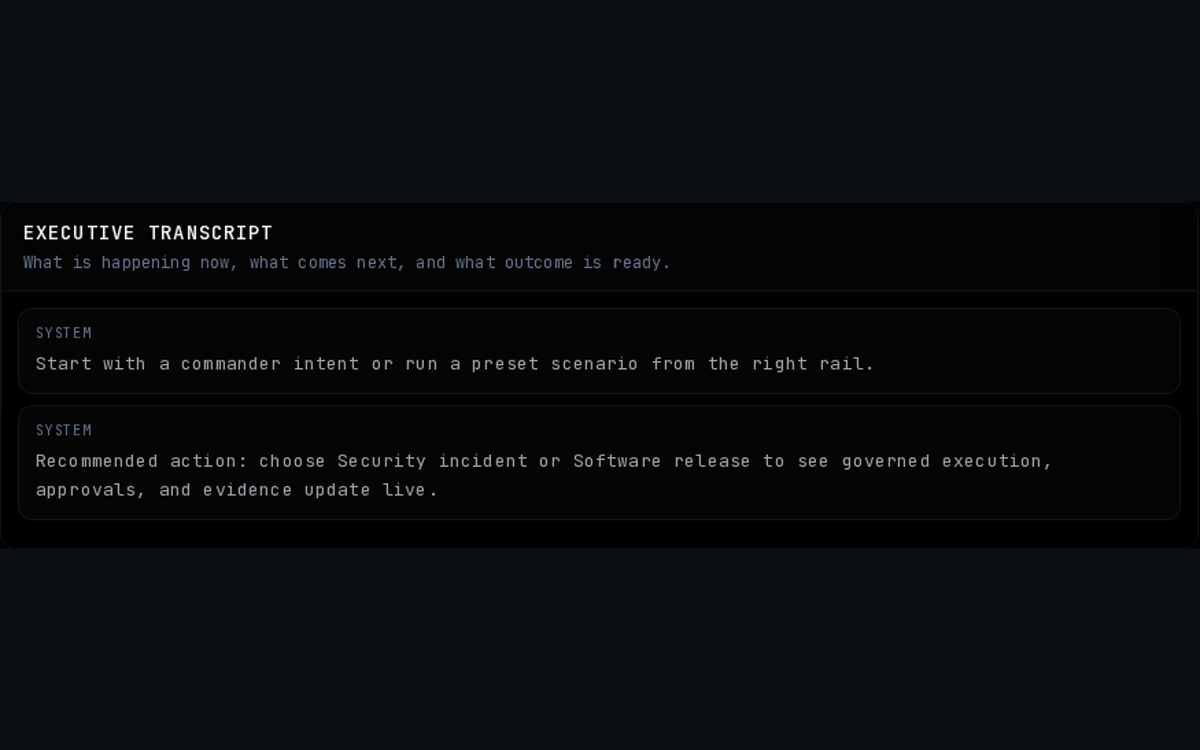
Runtime V3 shows the control layer in motion: mission posture, route ownership, policy-gated execution, and exportable evidence.
KRYFOR does not stop at execution logs. Each governed mission produces a structured decision record that can be reviewed, compared, and reused in later runs.
Governance proof
Runtime V3 exposes authority, escalation, and mission posture before the first tool call starts.
Route ownership proof
The mission topology makes routing, dependencies, and intervention points legible to operators and reviewers.
Execution proof
Web, browser, coding, and memory lanes execute with plain-language transcript output instead of opaque agent chatter.
Evidence proof
Every run closes with client-readable output, decision checkpoints, and evidence artifacts that can be exported or reviewed.
The first wedge is regulated operations where AI autonomy becomes valuable only when control, evidence, and accountability are explicit.
Security Operations Lead
Without KRYFOR: Alert overload and inconsistent escalation leave teams reacting too late.
With KRYFOR: KRYFOR routes triage, approvals, and evidence so response stays controlled under pressure.
Head of Risk
Without KRYFOR: Autonomous trading or risk actions can drift outside explicit policy and exposure limits.
With KRYFOR: KRYFOR enforces review gates, risk thresholds, and accountable decision ownership before execution.
Compliance Director
Without KRYFOR: Recurring regulatory workflows break when evidence, sign-off, and policy logic are fragmented.
With KRYFOR: KRYFOR standardizes routing, evidence capture, and approval control for auditable closure.
Platform Engineering Lead
Without KRYFOR: AI coding output becomes dangerous when release actions skip review, policy checks, or rollback logic.
With KRYFOR: KRYFOR turns coding missions into controlled delivery paths with deterministic release gates.
A governance layer that makes autonomous AI usable in regulated operations with deterministic routing, policy control, and audit-grade evidence.
Decision paths stay explicit across agent runs, escalation points, and executive ownership.
High-impact actions are bound by review logic before they touch production systems or customer operations.
Each mission ends with attributable decisions, evidence artifacts, and export-ready operating records.
Store policy-linked mission history as reusable decision records, not just raw logs.
The control layer stays abstract only until a mission starts. Then the path becomes explicit.
1. Signal arrives
2. AI drafts action
3. Risk policy checks limits
4. Auditor approves
5. Execution records evidence
1. Alert arrives
2. AI triages scope
3. Policy gates high-impact response
4. Lead approves path
5. Evidence closes incident
1. Request arrives
2. Architect plans change
3. Forge writes code
4. Sentinel checks release
5. Auditor approves outcome
1. Case opens
2. AI assembles record
3. Policy checks required proof
4. Reviewer signs off
5. Closure exports evidence
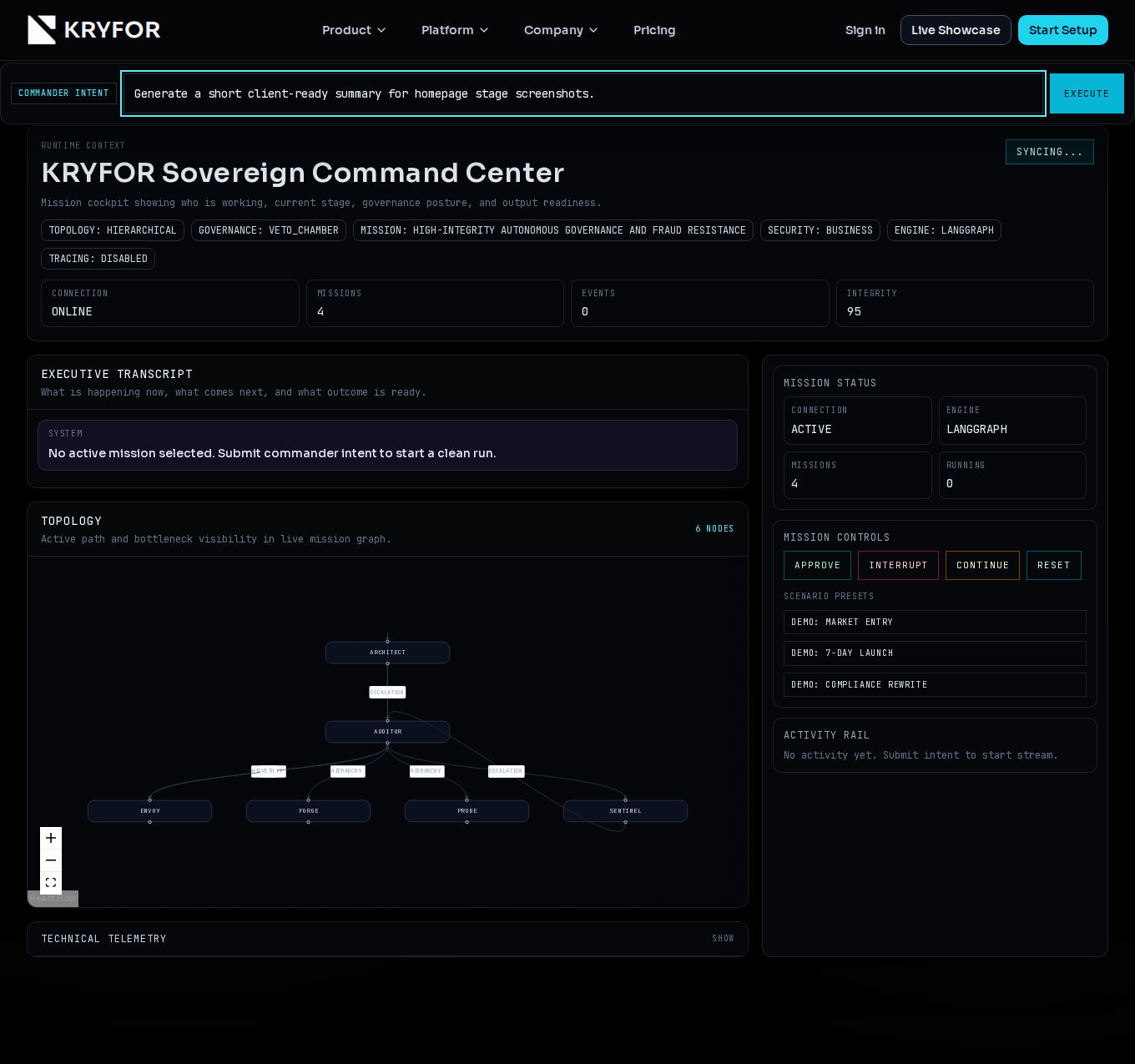
Select by deployment depth and governance requirements, not generic feature lists.
Community
$0
For internal validation and early proof of governed missions.
Professional
$79 / month
For teams running governed AI operations in production.
Enterprise
From $499 / month
For regulated environments, private rollout, and organization-scale control.
Buyers can map scope to mission volume, audit retention, and integration depth before procurement.
Scope KRYFOR for early governed trials and runtime validation.
Best fit for teams moving from proof to governed production operations.
Built for regulated environments with policy-specific controls and private rollout.
Extend runtime value with modular controls that directly improve evidence quality, risk routing, and regulated delivery.
Policy topology templates, approval matrices, and risk-routing presets by operating model.
Extended decision and audit retention with export-ready evidence bundles.
Regulatory reporting views, compliance-ready policy profiles, and review workflows.
Enterprise SSO/SIEM connectors, identity controls, and hardened access boundaries.
Once the core governance model is clear, KRYFOR expands across mission types and sectors.
Secondary path
Run one governed mission in Runtime V3, show controlled evidence, then route the buyer into setup or enterprise review.